New SEC Cybersecurity Rules Are Coming – The Time to Prepare is Now
Cyber risk for financial firms is about to get a lot more regulated. Announcing its most recent Regulatory Flex Agenda in June 2022, the U.S. Securities and Exchange Commission (SEC) revealed that it is moving quickly on its proposed Cybersecurity Risk Management Rules for investment advisers and funds, having scheduled the proposed rulemaking for a final vote by April 2023. In addition, the Office of Management and Budget website now shows that cybersecurity rules are currently in the final rule stage.
Rules expected to stay the course
Adoption of the cybersecurity rules is likely a foregone conclusion, given that nearly every rule considered by the Commission under the watch of SEC Chair Gary Gensler has proceeded along party lines, passing with votes of 3-1. If past voting records hint at their respective regulatory inclinations, the four senior Commissioners will likely continue to support Gensler’s agenda 3-1. Moreover, the recent swearing-in of Jaime Lizarraga to fill the vacant fifth seat is unlikely to derail the course charted by Gensler.
However, it is feasible that the Supreme Court’s recent decision in West Virginia v. EPA could open the door for any government agency regulations with a substantial economic impact to be challenged in court, but that remains to be seen.
Cybersecurity requirements for RIAs and funds
With the Cybersecurity Risk Management Rules heading towards the finish line, there will certainly be significant impacts on registered investment advisers (RIAs) and funds. The new rules, specifically rule 206(4)-9 under the Advisers Act and rule 38a-2 under the Investment Company Act, are designed to enhance cybersecurity practices among advisers and funds, and to increase the effectiveness of cybersecurity-related disclosures to clients and investors.
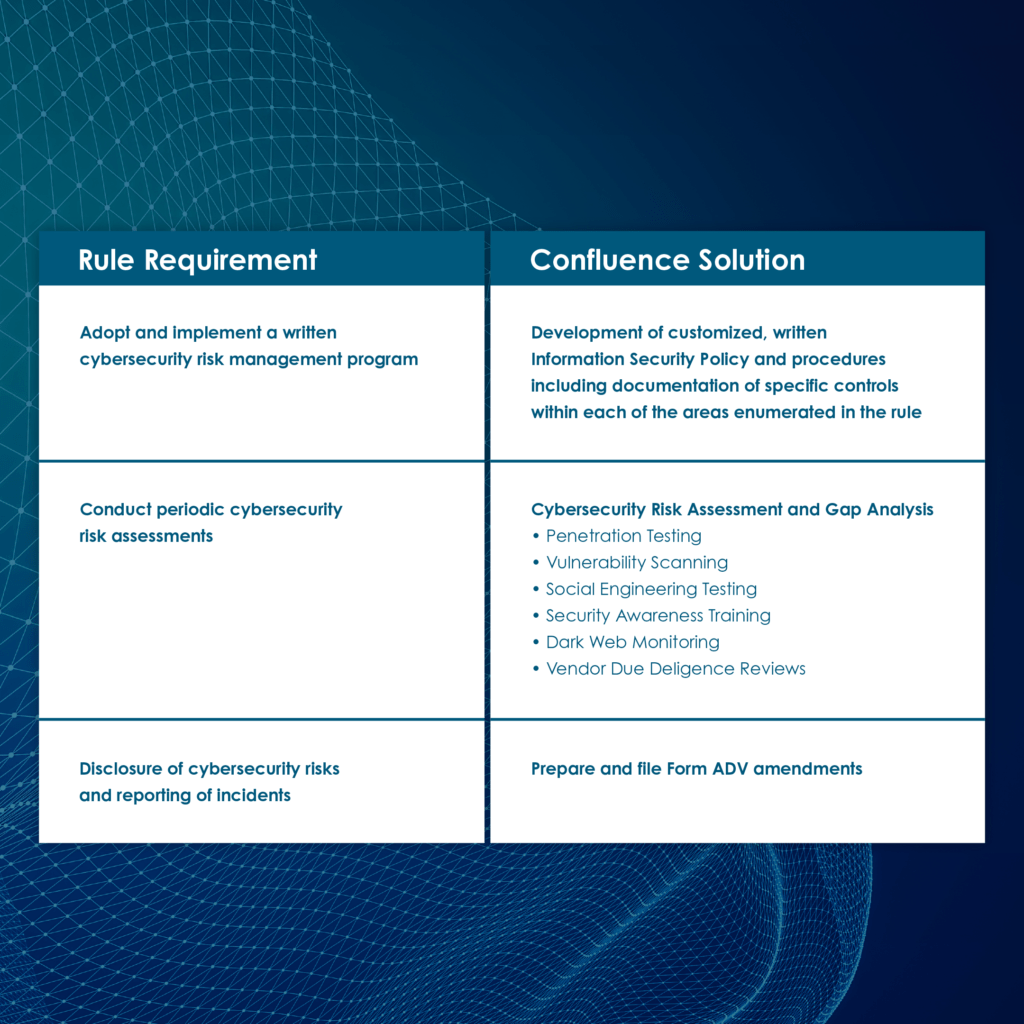
Under the proposed rules, advisers and funds would be required to:
- Adopt and implement a written cybersecurity risk management program that includes conducting periodic risk assessments and maintaining cyber risk inventories, evaluating user security and access, assessing information protection, managing threats and vulnerabilities, and addressing incident response and recovery. For funds, the rules will require the board of directors (including a majority of independent directors) to approve the Information Security Policy.
- Conduct a formal annual cyber review, similar to the annual compliance program review. This review will need to assess the design and effectiveness of cybersecurity policies and procedures and document them in a written report. The report should note, among other things, the review process, types of cyber testing conducted, results of such cyber testing, any cyber incidents occurring since the last review, and any material changes to policies and procedures. The rules would require this annual cyber report to be overseen by individuals who administer the firm’s cybersecurity policies and procedures. The SEC acknowledges that some firms do not have this expertise in-house and will need to outsource this review and report, but also encourages adviser/fund personnel to participate in the review. In addition, for funds, the rules will require the firm’s board of directors (including a majority of independent directors) to review the annual cyber review report.
- Disclose cybersecurity risks publicly on regulatory disclosure forms. For investment advisers, this disclosure should be added to Form ADV. The Form ADV Part 2A Brochure would include a new Item 20 (“Cybersecurity Risks and Incidents”). For funds, these risks should be reported on Forms N-1A, N-2, N-3, N-4, N-6, N-8B-2, and S-6.
All advisers would need to describe (1) cyber risks that could materially affect the adviser’s services and how the firm assesses, prioritizes, and addresses these cybersecurity risks, and (2) a description of any cyber incident that has occurred within the last two fiscal years that has “significantly disrupted or degraded” the firm’s critical operations, or has led to the unauthorized access or use of adviser information, resulting in substantial harm to the firm or its clients. In addition, specific information describing each incident would be required, including entities affected, dates, whether the incident is resolved or ongoing, whether data was stolen, altered, accessed, or used in an unauthorized manner, the effect of the incident on the firm’s operations, and whether the firm or any service provider has remediated the issue.
Changes to Rule 204-3 under the Advisers Act would also require ADV brochures to be delivered to clients promptly after an ADV amendment which adds or updates disclosure of an incident in Form ADV Part 2A Item 9 or Item 20.B or Form ADV Part 2B Item 3. Therefore, firms should be prepared to deliver an amended Form ADV to clients as part of their incident response.
- Maintain books and records under the new Advisers Act Rule 204-2(a)(17)(iv) through (vii), which includes copies of Form ADV-C disclosing cyber incidents, records documenting the occurrence of cyber incidents, and response and recovery steps taken within the prior five years, and records of all cyber risk assessments and testing conducted.
What cyber rule critics and supporters are saying
The comment period for the proposed rules has closed. While the public comments received to date are split for and against the new rules, it is worth noting that even the strongest criticisms – namely, those from the Investment Adviser Association (IAA) and the Investment Company Institute (ICI) – still support the rulemaking but take issue with the specific details.
The comments against the rule fall into the following main buckets:
- That the rule should not be grounded in the anti-fraud prohibitions of the Advisers Act, under the logic that advisers who experience a cyber breach are usually victims of the fraud and are not those who cause the fraud.
- That the cyber rules are very specific or prescriptive instead of principles-based, similar to the typical rules we see, and that existing rules already cover an obligation to address cyber risk. However, as the SEC noted in its cybersecurity risk alerts over the past several years, firms still have a long way to go in getting their cybersecurity programs up to speed, with numerous deficient and inadequate practices noted. Moreover, with FINRA, the Department of Labor, and several states already mandating specific cyber provisions, the SEC is increasingly in the minority of agencies without specific cyber rules.
- That the requirement that any contract with a service provider has to include specific language − whereby the service provider agrees to implement and maintain appropriate measures for cybersecurity − is too onerous, and therefore some service providers won’t sign those.
- That the cyber annual review should be part of the existing 206(4)-7 compliance annual review rather than its separate review and report.
- That the 48-hour incident reporting deadline is too short and should be 72 hours instead, similar to the reporting deadline under GDPR, because 48 hours isn’t enough time to fully figure out what happened. These commenters also suggest that firms should spend their initial 48 hours on containment and getting back to managing portfolios rather than filling out forms to help the SEC identify patterns and trends.
Commenters who support the rule:
- Want an exemption for smaller advisers. However, they disagree on whether “small” means five employees or 50 or whether it means $100 million in AUM or a larger threshold. Other commenters argued for an exemption for advisers with little to no personally identifiable information about individuals (e.g., pension consultants and institutional advisers).
- Want the ability of fund boards to rely on cyber assessments conducted by third parties.
- Are primarily from the general investing public and individual investors who want higher fines and more penalties when their data is compromised due to their financial institution getting hacked.
Mitigating cyber risk is good business
Cyber risk is business risk. Even in the absence of a regulatory requirement, investment advisers and funds have fiduciary duties that support protecting client and investor information. As a result, advisers and funds are significant targets for malicious actors. They face substantial reputational risk by not implementing comprehensive information security policies, procedures, and controls or by not conducting regular cyber risk assessments, testing, and training.
Confluence’s cybersecurity services and solutions are designed to help firms address their cyber risks and the impending regulatory requirements under the new Cybersecurity Risk Management Rules. Firms should begin planning now to get their cyber ducks in a row.
To learn more about how our solutions can help lower your cyber risk, please contact us at cybersecurity@cssregtech.com.
Subscribe today and receive our latest industry updates and articles.
You may unsubscribe at anytime with our simple “unsubscribe” link at the bottom of each communication. Please see our privacy notices below for further information, including a list of affiliates covered by this consent.